- Main
- Mathematics
- Cryptography: Theory and Practice

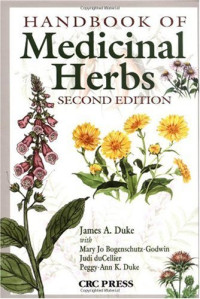
Cryptography: Theory and Practice
Douglas R. Stinson, Maura B. Patersonこの本はいかがでしたか?
ファイルの質はいかがですか?
質を評価するには、本をダウンロードしてください。
ダウンロードしたファイルの質はいかがでしたか?
Through three editions, Cryptography: Theory and Practice, has been embraced by instructors and students alike. It offers a comprehensive primer for the subject’s fundamentals while presenting the most current advances in cryptography.
The authors offer comprehensive, in-depth treatment of the methods and protocols that are vital to safeguarding the seemingly infinite and increasing amount of information circulating around the world.
Key Features of the Fourth Edition:
• New chapter on the exciting, emerging new area of post-quantum cryptography (Chapter 9).
• New high-level, nontechnical overview of the goals and tools of cryptography (Chapter 1).
• New mathematical appendix that summarizes definitions and main results on number theory and algebra (Appendix A).
• An expanded treatment of stream ciphers, including common design techniques along with coverage of Trivium.
• Interesting attacks on cryptosystems, including: padding oracle attack, correlation attacks and algebraic attacks on stream ciphers, attack on the DUAL-EC random bit generator that makes use of a trapdoor.
• A treatment of the sponge construction for hash functions and its use in the new SHA-3 hash standard.
• Methods of key distribution in sensor networks.
• The basics of visual cryptography, allowing a secure method to split a secret visual message into pieces (shares) that can later be combined to reconstruct the secret.
• The fundamental techniques cryptocurrencies, as used in Bitcoin and blockchain.
• The basics of the new methods employed in messaging protocols such as Signal, including deniability and Diffie-Hellman key ratcheting.
The authors offer comprehensive, in-depth treatment of the methods and protocols that are vital to safeguarding the seemingly infinite and increasing amount of information circulating around the world.
Key Features of the Fourth Edition:
• New chapter on the exciting, emerging new area of post-quantum cryptography (Chapter 9).
• New high-level, nontechnical overview of the goals and tools of cryptography (Chapter 1).
• New mathematical appendix that summarizes definitions and main results on number theory and algebra (Appendix A).
• An expanded treatment of stream ciphers, including common design techniques along with coverage of Trivium.
• Interesting attacks on cryptosystems, including: padding oracle attack, correlation attacks and algebraic attacks on stream ciphers, attack on the DUAL-EC random bit generator that makes use of a trapdoor.
• A treatment of the sponge construction for hash functions and its use in the new SHA-3 hash standard.
• Methods of key distribution in sensor networks.
• The basics of visual cryptography, allowing a secure method to split a secret visual message into pieces (shares) that can later be combined to reconstruct the secret.
• The fundamental techniques cryptocurrencies, as used in Bitcoin and blockchain.
• The basics of the new methods employed in messaging protocols such as Signal, including deniability and Diffie-Hellman key ratcheting.
カテゴリー:
年:
2018
版:
4
出版社:
CRC Press
言語:
english
ページ:
598
ISBN 10:
1138197017
ISBN 13:
9781138197015
シリーズ:
Textbooks in Mathematics
ファイル:
PDF, 22.74 MB
あなたのタグ:
IPFS:
CID , CID Blake2b
english, 2018
オンラインで読む
- ダウンロード
- pdf 22.74 MB Current page
- Checking other formats...
- 変換する
- 8 MBを超えるファイルの変換を解禁するPremium
1~5分以内にこのファイルをあなたの電子メールにお届けします。
ファイルはTelegramメッセンジャー経由で送信されます。受け取るまでに1〜5分かかる場合があります。
注意:Z-LibraryのTelegramボットにアカウントをリンクさせていることを確認してください。
ファイルはKindleアカウントに送信されます。受け取るまでに1〜5分かかる場合があります。
注意!Kindleへ送信するすべての本は、メールによる確認が求められています。Amazon Kindle Supportからメールが送信されますので、メールをご確認ください。
への変換進行中。
への変換が失敗しました。
主要なフレーズ
関連ブックリスト


































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org  ファイル拡張子変換機能
ファイル拡張子変換機能 検索結果をもっと見る
検索結果をもっと見る その他多くの特典
その他多くの特典